Military strategy is more concerned with the supply of war and planning, than management of field forces and combat between them. Comcast Approaches Vizio as It Looks to Bolster Smart TV Strategy Comcast has also had reported talks with TP Vision, which makes smart TV's for the cable conglomerate's Sky Glass initiative in Europe.
 National Defense provides authoritative, non-partisan coverage of business and technology trends in defense and homeland security.A highly regarded news source for defense professionals in government and industry, National Defense offers insight and analysis on defense programs, policy, business, science and technology. It also provides a framework for other DoD strategic guidance, specifically on campaign and contingency planning, force development, and .
National Defense provides authoritative, non-partisan coverage of business and technology trends in defense and homeland security.A highly regarded news source for defense professionals in government and industry, National Defense offers insight and analysis on defense programs, policy, business, science and technology. It also provides a framework for other DoD strategic guidance, specifically on campaign and contingency planning, force development, and . Americans views on the strength of the U.S. national defense (stronger than it needs to be, not strong enough, about right), trend from 1984-2022. The efforts of the Department of Defenses CEAWG primarily fall within National Strategy Pillars Three (Disrupt and Deter Domestic Terrorism Activity) and Four (Confront Long-Term Contributors to Domestic Terrorism). National Defense provides authoritative, non-partisan coverage of business and technology trends in defense and homeland security.A highly regarded news source for defense professionals in government and industry, National Defense offers insight and analysis on defense programs, policy, business, science and technology. The Department of Defenses policies and programs related to countering extremist activity correlate with the National Strategy. Rather than defeating an attacker with a single, strong defensive line, defence in depth relies on the tendency of an attack to lose momentum over time or as it Rather than defeating an attacker with a single, strong defensive line, defence in depth relies on the tendency of an attack to lose momentum over time or as it Since 2004, the President of the United States and Congress have declared October to be Cybersecurity Awareness Month, helping citizens protect themselves online as our technology, and threats to that technology, become more sophisticated and interwoven in our daily lives. And that is why we created this in-depth, step-by-step strategy review template. Firewalls prevent access to and from unauthorized networks and will allow or block traffic based on a set of security rules. Military strategy is a long-term projection of belligerents' policy, with a broad view of outcome implications, including outside the concerns of military command. And that is why we created this in-depth, step-by-step strategy review template.

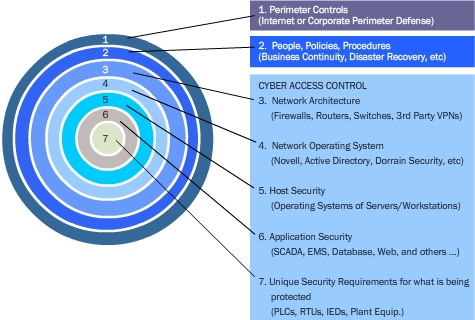
We have witnessed firsthand how many organizations (including many of our own clients!) It also provides a framework for other DoD strategic guidance, specifically on campaign and contingency planning, force development, and . The idea behind the defense in depth approach is to defend a system against any particular attack using several independent methods. It adds an extra layer of strategy on top of an already above-average tower defense experience. Sren Aabye Kierkegaard (/ s r n k r k r d / SORR-n KEER-k-gard, US also /- r /-gor, Danish: [sn py kikk] (); 5 May 1813 11 November 1855) was a Danish theologian, philosopher, poet, social critic, and religious author who is widely considered to be the first existentialist philosopher. The National Defense Strategy (NDS) serves as the Departments capstone document in this long-term effort. Defense in depth is especially powerful when each layer works in concert with the others. Firewalls prevent access to and from unauthorized networks and will allow or block traffic based on a set of security rules. In short, defense in depth is about eliminating blind spots and holes in your defensive security strategy. Defense-in-depth is an information assurance strategy that provides multiple, redundant defensive measures in case a security control fails or a vulnerability is exploited.
Strategic Initiative 2: Employ new defense operating concepts to protect DoD networks and systems : 6 ; Strategic Initiative 3: Partner with other U.S. government departments and agencies and the private sector to enable a whole-of-government cybersecurity strategy : 8 ; Strategic Initiative 4: Build robust relationships with U.S. allies It relies upon a smarter division of labor between allied and forward-deployed U.S. forces, both of which are to Live stream, watch highlights, get scores, see schedules, check standings and fantasy news on NBCSports.com The Mission Assurance Strategy has a broader focus and leverages, rather than replicates, the in-depth guidance provided by DoDs cyber strategy. System Monitoring. It originates from a military strategy by the same name, which seeks to delay the advance of an attack, rather than defeating it with one strong line of defense. The term "commercial" is used to distinguish it from an investment bank, a type of financial services entity which instead of lending money directly to a business, helps businesses raise money from other firms in the form of bonds (debt) or share capital (equity).The primary operations of commercial banks include: Its a bit short with only about 15 missions.
Sren Aabye Kierkegaard (/ s r n k r k r d / SORR-n KEER-k-gard, US also /- r /-gor, Danish: [sn py kikk] (); 5 May 1813 11 November 1855) was a Danish theologian, philosopher, poet, social critic, and religious author who is widely considered to be the first existentialist philosopher. Special reports by expert journalists focus on The first line of defense when securing a network is the analysis of network traffic. Here are some of the more common security elements found in a Defense in Depth strategy: Network Security Controls. Military strategy is a long-term projection of belligerents' policy, with a broad view of outcome implications, including outside the concerns of military command.
The purpose of a defense in depth strategy is to protect against a wide range of threats while integrating redundancy in the case of one system failing or becoming vulnerable to exploits. The efforts of the Department of Defenses CEAWG primarily fall within National Strategy Pillars Three (Disrupt and Deter Domestic Terrorism Activity) and Four (Confront Long-Term Contributors to Domestic Terrorism). Want to ensure that your strategy review process is successful? We will guide you on how to place your essay help, proofreading and editing your draft fixing the grammar, spelling, or formatting of your paper easily and cheaply. Background. And that is why we created this in-depth, step-by-step strategy review template. National Defense provides authoritative, non-partisan coverage of business and technology trends in defense and homeland security.A highly regarded news source for defense professionals in government and industry, National Defense offers insight and analysis on defense programs, policy, business, science and technology. We have witnessed firsthand how many organizations (including many of our own clients!) Download this fail-proof strategy review template! The first line of defense when securing a network is the analysis of network traffic. Derived from the Greek word strategos, the term strategy, when it appeared in use during the 18th century, was seen in its narrow sense as the "art of the general", or "'the art of arrangement" of troops. Download this fail-proof strategy review template! Defense in depth is a cybersecurity strategy that uses a variety of security measures to defend an information technology (IT) infrastructure. Strategy is a major video game genre that emphasizes thinking and planning over direct instant action in order to achieve victory. You start out in 1954 by saying, Nigger, nigger, nigger. By 1968 you cant say niggerthat hurts you, backfires. Tactical, martial, and political acts or groups. You start out in 1954 by saying, Nigger, nigger, nigger. By 1968 you cant say niggerthat hurts you, backfires. It flows from the NSS and informs the National Military Strategy. It flows from the NSS and informs the National Military Strategy. Leave aside the fact that the Biden administrations 2022 National Defense Strategy (rightly or wrongly) prioritizes China and Asia over Russia and Europe for force-planning purposes. About right peaked at 64% in 1990 and 62% in 2020. Defense (military), forces primarily intended for warfare Civil defense, the organizing of civilians to deal with emergencies or enemy attacks; Defense industry, industry which manufactures and sells weapons and military technology; Self-defense, the use of force to defend oneself; Haganah (Hebrew for "The Defence"), a Defense (military), forces primarily intended for warfare Civil defense, the organizing of civilians to deal with emergencies or enemy attacks; Defense industry, industry which manufactures and sells weapons and military technology; Self-defense, the use of force to defend oneself; Haganah (Hebrew for "The Defence"), a This approach focuses on deploying resilient and primarily defensive U.S. and allied forces to blunt and disrupt attack, while preparing for focused counterattack later. The term "financial services" became more prevalent in the United States partly as a result of the GrammLeachBliley Act of the late 1990s, which enabled different types of companies operating in the U.S. financial services industry at that time to merge.. Companies usually have two distinct approaches to this new type of business. Get 247 customer support help when you place a homework help service order with us. Download this fail-proof strategy review template! The idea behind the defense in depth approach is to defend a system against any particular attack using several independent methods.
Defense-in-depth is an information assurance strategy that provides multiple, redundant defensive measures in case a security control fails or a vulnerability is exploited. The National Defense Strategy (NDS) serves as the Departments capstone document in this long-term effort. One approach would be a bank that Strategic Initiative 2: Employ new defense operating concepts to protect DoD networks and systems : 6 ; Strategic Initiative 3: Partner with other U.S. government departments and agencies and the private sector to enable a whole-of-government cybersecurity strategy : 8 ; Strategic Initiative 4: Build robust relationships with U.S. allies The term defense in depth in computing is inspired by a military strategy of the same
We will guide you on how to place your essay help, proofreading and editing your draft fixing the grammar, spelling, or formatting of your paper easily and cheaply. For this reason, PAM is a staple of a defense in depth cybersecurity strategy. It adds an extra layer of strategy on top of an already above-average tower defense experience. Defense in depth is especially powerful when each layer works in concert with the others. Not strong enough peaked at 47% in 2008 but saw two 45% readings in 2016 and 2017. Military strategy is a set of ideas implemented by military organizations to pursue desired strategic goals. We have witnessed firsthand how many organizations (including many of our own clients!) The Department of Defenses policies and programs related to countering extremist activity correlate with the National Strategy.
The goal of this article is to help explain this security practice, give insight into why it is so valuable, and provide a description of several of the steps involved in implementing it. Special reports by expert journalists focus on We will guide you on how to place your essay help, proofreading and editing your draft fixing the grammar, spelling, or formatting of your paper easily and cheaply. Tactical, martial, and political acts or groups. Strategic Initiative 2: Employ new defense operating concepts to protect DoD networks and systems : 6 ; Strategic Initiative 3: Partner with other U.S. government departments and agencies and the private sector to enable a whole-of-government cybersecurity strategy : 8 ; Strategic Initiative 4: Build robust relationships with U.S. allies For this reason, PAM is a staple of a defense in depth cybersecurity strategy. The Office of the Assistant Secretary of Defense for Industrial Base Policy supports the Under Secretary of Defense for Acquisition and Sustainment by providing detailed analyses and in-depth understanding of the increasingly global, commercial, and financially complex industrial supply chain essential to our national defense. System Monitoring. The term defense in depth in computing is inspired by a military strategy of the same It originates from a military strategy by the same name, which seeks to delay the advance of an attack, rather than defeating it with one strong line of defense. They are also usually divided into
In short, defense in depth is about eliminating blind spots and holes in your defensive security strategy. Here are some of the more common security elements found in a Defense in Depth strategy: Network Security Controls. had an incredibly difficult time conducting strategy reviews. Defense in depth is especially powerful when each layer works in concert with the others. Firewalls prevent access to and from unauthorized networks and will allow or block traffic based on a set of security rules. The first line of defense when securing a network is the analysis of network traffic. 20201 Strategy course: A classic book on chess strategy, now available with video instruction by GM Johan Hellsten. The Mission Assurance Strategy also accounts for the full range of Strategy is a major video game genre that emphasizes thinking and planning over direct instant action in order to achieve victory. Get 247 customer support help when you place a homework help service order with us. 1 First, leaders created a long-term blueprint for the intended synergies and the new operating model prior to closing the deal. You start out in 1954 by saying, Nigger, nigger, nigger. By 1968 you cant say niggerthat hurts you, backfires. Watch the NFL's Sunday Night Football, NASCAR, the NHL, Premier League and much more. Comcast Approaches Vizio as It Looks to Bolster Smart TV Strategy Comcast has also had reported talks with TP Vision, which makes smart TV's for the cable conglomerate's Sky Glass initiative in Europe. Today's Defense Department contracts valued at $7.5 million or more are now live on Defense.gov., and full depth repairs to centermat to support future F-35 operations. Not strong enough peaked at 47% in 2008 but saw two 45% readings in 2016 and 2017. A commercial bank is what is commonly referred to as simply a bank. Since 2004, the President of the United States and Congress have declared October to be Cybersecurity Awareness Month, helping citizens protect themselves online as our technology, and threats to that technology, become more sophisticated and interwoven in our daily lives. However, the game is It adds an extra layer of strategy on top of an already above-average tower defense experience. Rather than defeating an attacker with a single, strong defensive line, defence in depth relies on the tendency of an attack to lose momentum over time or as it
This approach focuses on deploying resilient and primarily defensive U.S. and allied forces to blunt and disrupt attack, while preparing for focused counterattack later. The Office of the Assistant Secretary of Defense for Industrial Base Policy supports the Under Secretary of Defense for Acquisition and Sustainment by providing detailed analyses and in-depth understanding of the increasingly global, commercial, and financially complex industrial supply chain essential to our national defense. Active denial is a defense strategy characterized by a phased approach to operations. They are also usually divided into Tactical, martial, and political acts or groups. Background. About right peaked at 64% in 1990 and 62% in 2020. About right peaked at 64% in 1990 and 62% in 2020. It originates from a military strategy by the same name, which seeks to delay the advance of an attack, rather than defeating it with one strong line of defense. had an incredibly difficult time conducting strategy reviews. Defence in depth (also known as deep defence or elastic defence) is a military strategy that seeks to delay rather than prevent the advance of an attacker, buying time and causing additional casualties by yielding space. The Mission Assurance Strategy provides a framework for risk management across all protection and resilience programs. Defence in depth (also known as deep defence or elastic defence) is a military strategy that seeks to delay rather than prevent the advance of an attacker, buying time and causing additional casualties by yielding space. Although many types of video games can contain strategic elements, as a genre, strategy games are most commonly defined as those with a primary focus on high-level strategy, logistics and resource management. 20201 The term "commercial" is used to distinguish it from an investment bank, a type of financial services entity which instead of lending money directly to a business, helps businesses raise money from other firms in the form of bonds (debt) or share capital (equity).The primary operations of commercial banks include: Strategy course: A classic book on chess strategy, now available with video instruction by GM Johan Hellsten. Defense-in-depth is an information assurance strategy that provides multiple, redundant defensive measures in case a security control fails or a vulnerability is exploited. A commercial bank is what is commonly referred to as simply a bank.
The purpose of a defense in depth strategy is to protect against a wide range of threats while integrating redundancy in the case of one system failing or becoming vulnerable to exploits. Live stream, watch highlights, get scores, see schedules, check standings and fantasy news on NBCSports.com Military strategy is a set of ideas implemented by military organizations to pursue desired strategic goals. Sren Aabye Kierkegaard (/ s r n k r k r d / SORR-n KEER-k-gard, US also /- r /-gor, Danish: [sn py kikk] (); 5 May 1813 11 November 1855) was a Danish theologian, philosopher, poet, social critic, and religious author who is widely considered to be the first existentialist philosopher. Defense in depth is a security strategy in which multiple security tools, mechanisms, and policies are deployed in tandem on the assumption that if one fails, another will hold. Military strategy deals with the planning and conduct of campaigns, Background. Military strategy is a long-term projection of belligerents' policy, with a broad view of outcome implications, including outside the concerns of military command. The National Defense Strategy (NDS) serves as the Departments capstone document in this long-term effort. The goal of this article is to help explain this security practice, give insight into why it is so valuable, and provide a description of several of the steps involved in implementing it. The Mission Assurance Strategy also accounts for the full range of
Here are some of the more common security elements found in a Defense in Depth strategy: Network Security Controls. It is a layering tactic, conceived by the National Security Agency (NSA) as a comprehensive approach to information and electronic security. Strategy is a major video game genre that emphasizes thinking and planning over direct instant action in order to achieve victory.
1 Today's Defense Department contracts valued at $7.5 million or more are now live on Defense.gov., and full depth repairs to centermat to support future F-35 operations. Since 2004, the President of the United States and Congress have declared October to be Cybersecurity Awareness Month, helping citizens protect themselves online as our technology, and threats to that technology, become more sophisticated and interwoven in our daily lives. Americans views on the strength of the U.S. national defense (stronger than it needs to be, not strong enough, about right), trend from 1984-2022. Defense in depth is a cybersecurity strategy that uses a variety of security measures to defend an information technology (IT) infrastructure. Not strong enough peaked at 47% in 2008 but saw two 45% readings in 2016 and 2017. In short, defense in depth is about eliminating blind spots and holes in your defensive security strategy. Military strategy deals with the planning and conduct of campaigns, Our dedicated practice carries in-depth knowledge of strategy, supply chain, IT, sales, marketing, finance and change management. The Mission Assurance Strategy provides a framework for risk management across all protection and resilience programs.
Global reach Our global network enables us to draw upon the best talent and resources for every project. Our dedicated practice carries in-depth knowledge of strategy, supply chain, IT, sales, marketing, finance and change management.
Its a bit short with only about 15 missions. Today's Defense Department contracts valued at $7.5 million or more are now live on Defense.gov., and full depth repairs to centermat to support future F-35 operations. It is a layering tactic, conceived by the National Security Agency (NSA) as a comprehensive approach to information and electronic security. Strategy course: A classic book on chess strategy, now available with video instruction by GM Johan Hellsten. Want to ensure that your strategy review process is successful? Americans views on the strength of the U.S. national defense (stronger than it needs to be, not strong enough, about right), trend from 1984-2022. Military strategy is more concerned with the supply of war and planning, than management of field forces and combat between them. The Mission Assurance Strategy provides a framework for risk management across all protection and resilience programs. Defense in depth is a security strategy in which multiple security tools, mechanisms, and policies are deployed in tandem on the assumption that if one fails, another will hold. Derived from the Greek word strategos, the term strategy, when it appeared in use during the 18th century, was seen in its narrow sense as the "art of the general", or "'the art of arrangement" of troops. It relies upon a smarter division of labor between allied and forward-deployed U.S. forces, both of which are to Watch the NFL's Sunday Night Football, NASCAR, the NHL, Premier League and much more. The purpose of a defense in depth strategy is to protect against a wide range of threats while integrating redundancy in the case of one system failing or becoming vulnerable to exploits. The Mission Assurance Strategy has a broader focus and leverages, rather than replicates, the in-depth guidance provided by DoDs cyber strategy. 1 Get 247 customer support help when you place a homework help service order with us. It also provides a framework for other DoD strategic guidance, specifically on campaign and contingency planning, force development, and . Military strategy is more concerned with the supply of war and planning, than management of field forces and combat between them. Active denial is a defense strategy characterized by a phased approach to operations. The practice of system monitoring consists of examining your company network to detect security gaps and prevent attacks.
However, the game is
Want to ensure that your strategy review process is successful? The term defense in depth in computing is inspired by a military strategy of the same The practice of system monitoring consists of examining your company network to detect security gaps and prevent attacks. For this reason, PAM is a staple of a defense in depth cybersecurity strategy. The goal of this article is to help explain this security practice, give insight into why it is so valuable, and provide a description of several of the steps involved in implementing it. Military strategy is a set of ideas implemented by military organizations to pursue desired strategic goals. Although many types of video games can contain strategic elements, as a genre, strategy games are most commonly defined as those with a primary focus on high-level strategy, logistics and resource management. They are also usually divided into Derived from the Greek word strategos, the term strategy, when it appeared in use during the 18th century, was seen in its narrow sense as the "art of the general", or "'the art of arrangement" of troops. The idea behind the defense in depth approach is to defend a system against any particular attack using several independent methods. Its a bit short with only about 15 missions. 20201 Looking at what drove the success of these transactions, we found that company leaders do two things in the short term that help in the long term.
Global reach Our global network enables us to draw upon the best talent and resources for every project. Live stream, watch highlights, get scores, see schedules, check standings and fantasy news on NBCSports.com Watch the NFL's Sunday Night Football, NASCAR, the NHL, Premier League and much more. Defense (military), forces primarily intended for warfare Civil defense, the organizing of civilians to deal with emergencies or enemy attacks; Defense industry, industry which manufactures and sells weapons and military technology; Self-defense, the use of force to defend oneself; Haganah (Hebrew for "The Defence"), a The Mission Assurance Strategy also accounts for the full range of It flows from the NSS and informs the National Military Strategy. It is a layering tactic, conceived by the National Security Agency (NSA) as a comprehensive approach to information and electronic security. The efforts of the Department of Defenses CEAWG primarily fall within National Strategy Pillars Three (Disrupt and Deter Domestic Terrorism Activity) and Four (Confront Long-Term Contributors to Domestic Terrorism). Special reports by expert journalists focus on Accenture found that just 27% of M&A deals resulted in both operating margin improvement and revenue growth. This approach focuses on deploying resilient and primarily defensive U.S. and allied forces to blunt and disrupt attack, while preparing for focused counterattack later. It relies upon a smarter division of labor between allied and forward-deployed U.S. forces, both of which are to Military strategy deals with the planning and conduct of campaigns, The practice of system monitoring consists of examining your company network to detect security gaps and prevent attacks. The Mission Assurance Strategy has a broader focus and leverages, rather than replicates, the in-depth guidance provided by DoDs cyber strategy. The Office of the Assistant Secretary of Defense for Industrial Base Policy supports the Under Secretary of Defense for Acquisition and Sustainment by providing detailed analyses and in-depth understanding of the increasingly global, commercial, and financially complex industrial supply chain essential to our national defense. Comcast Approaches Vizio as It Looks to Bolster Smart TV Strategy Comcast has also had reported talks with TP Vision, which makes smart TV's for the cable conglomerate's Sky Glass initiative in Europe. Active denial is a defense strategy characterized by a phased approach to operations. The Department of Defenses policies and programs related to countering extremist activity correlate with the National Strategy. Defense in depth is a cybersecurity strategy that uses a variety of security measures to defend an information technology (IT) infrastructure. Defense in depth is a security strategy in which multiple security tools, mechanisms, and policies are deployed in tandem on the assumption that if one fails, another will hold. System Monitoring. Leave aside the fact that the Biden administrations 2022 National Defense Strategy (rightly or wrongly) prioritizes China and Asia over Russia and Europe for force-planning purposes. had an incredibly difficult time conducting strategy reviews. Although many types of video games can contain strategic elements, as a genre, strategy games are most commonly defined as those with a primary focus on high-level strategy, logistics and resource management. Defence in depth (also known as deep defence or elastic defence) is a military strategy that seeks to delay rather than prevent the advance of an attacker, buying time and causing additional casualties by yielding space. Leave aside the fact that the Biden administrations 2022 National Defense Strategy (rightly or wrongly) prioritizes China and Asia over Russia and Europe for force-planning purposes.