In order to post comments, please make sure JavaScript and Cookies are enabled, and reload the page. The 'Use New Event Log API' option is now turned on by default. | eval User=lower(User) To configure Windows audit policy for SEM, you first need to modify the Windows audit policy using group policy at the domain controller and domain levels, so SEM can collect logs from your Windows system.
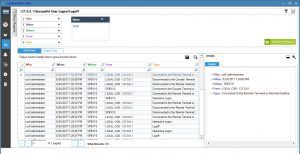
 Renew to download the latest product features, get 24/7 tech support, and access to instructor-led training. Why? A graphical display with detailed events summary lists the audit information for the selected period.
Renew to download the latest product features, get 24/7 tech support, and access to instructor-led training. Why? A graphical display with detailed events summary lists the audit information for the selected period. A logon (or logoff) event is an instance where a user logs into (or out) of a server. Under Domain Controllers node, right-click any customized policy. This utility works on Windows Vista/7/8/2008/10. The following article will help you to track users logon/logoff. This audit logon tool can allow admins to search for specific logon/logoff activity and monitor relevant event logs for unusual user account activity. But as I posted the output is far from being what is wanted. Get help, be heard by us and do your job better using our products. https://answers.splunk.com/answers/597752/report-for-showing-users-logon-logoff-and-the-dura.html, DLL Serach Oreder Hijacking (mitre : T1574.001), Search for disabled AD accounts that have been re-enabled. Connect with more than 150,000+ community members. Your daily dose of tech news, in brief. How do I audit account logon events in Security Event Manager? Open Filter Current Log on the rightmost pane and set filters for the following Event IDs. After you finish the translation, Run WinLogOnView, and all translated 12/11/17 20:43:03 12/11/17 20:43:14 0h 0m 11s john.doe PrimaryDC The
Learn through self-study, instructor-led, and on-demand classes with the SolarWinds Academy.
 Currently you have JavaScript disabled. Accelerates the identification and getting to the root cause of application performance issues. Keep track of logon and logoff events with a centralized logon audit events monitor. All rights reserved. The free utility I found eventcombMT will gather the information and is easy to use but as I noted it does a horrible job of parsing. Logon IDs are only unique between reboots on the same computer.". With SEM, you can also easily schedule these built-in or customized reports to automatically run and send reports to the correct recipients. This tool is based on the security event log of Windows, and the accuracy of the displayed information depends on the availability and accuracy of the data stored inside the security event log. The easiest and more efficient way to audit the same with Lepide Active Directory Auditor has also been explained. And he never married Pocahontas. In any case, I believe the events you are interested in will be on the workstations' Security Event Logs rather than the Domain Controllers' unless the users logged on to the Domain Controllers interactively or through RDP, in which case those events would be on the Domain Controller.
Currently you have JavaScript disabled. Accelerates the identification and getting to the root cause of application performance issues. Keep track of logon and logoff events with a centralized logon audit events monitor. All rights reserved. The free utility I found eventcombMT will gather the information and is easy to use but as I noted it does a horrible job of parsing. Logon IDs are only unique between reboots on the same computer.". With SEM, you can also easily schedule these built-in or customized reports to automatically run and send reports to the correct recipients. This tool is based on the security event log of Windows, and the accuracy of the displayed information depends on the availability and accuracy of the data stored inside the security event log. The easiest and more efficient way to audit the same with Lepide Active Directory Auditor has also been explained. And he never married Pocahontas. In any case, I believe the events you are interested in will be on the workstations' Security Event Logs rather than the Domain Controllers' unless the users logged on to the Domain Controllers interactively or through RDP, in which case those events would be on the Domain Controller. Our domain controllers did not have large enough event log file size settings to allow storing many weeks or months of login/logoff activity. Integrates with SolarWinds Service Desk, On-Premises Remote Support Software with FIPS 140-2 encryption standards.
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type. Ish. I'm trying to build a report to show user' logon and logoff times along with duration they were logged on and from source computer. Fixed bug: WinLogOnView failed to remember the last size/position of the main window if it was not located in the primary monitor. For example, I would like to know the logon and logoff dates and times of a user (we'll use the fictitious user John Smith in this example) and it would be nice if I received a report like this: DATE TIME EVENT USER COMPUTER04/01/2015 08:23 AM Logon jsmith smithj04/01/2015 04:18 PM Logoff jsmith smithj04/02/2015 10:11 AM Logon jsmith smithj04/02/2015 03:51 PM Logoff jsmith smithj. Even with this you'll have some considerations, like if the user is remote & accessing the network via VPN, if you're trying to account for BYOD, etc.
 An intuitive, integrated, and automated ITIL-ready IT service management (ITSM) solution that optimizes productivity. 12/11/17 21:46:30 12/11/17 21:46:30 0h 0m 0s john.doe PrimaryDC
An intuitive, integrated, and automated ITIL-ready IT service management (ITSM) solution that optimizes productivity. 12/11/17 21:46:30 12/11/17 21:46:30 0h 0m 0s john.doe PrimaryDC With a cutting-edge auditing solution, like Lepide Active Directory Auditor (part of Lepide Data Security Platform), monitoring and controlling the network activities of your organization is simple. Microsoft corporation and/or its respective suppliers make no representations about the suitability, reliability, or accuracy of the information and related graphics contained herein. In Security Filtering section in the right pane, click Add to add Everyone for applying this policy to all Active Directory objects. 12/11/17 16:28:28 12/11/17 16:38:41 0h 10m 13s john.doe PrimaryDC Report for showing users logon / logoff and the du https://answers.splunk.com/answers/462736/report-to-monitor-logonlogoff-time-and-duration-on.html, https://answers.splunk.com/answers/511064/how-do-i-chart-windows-logon-and-logoff-per-user-b.html. names, product names, or trademarks belong to their respective owners. | transaction User maxevents=2 startswith="EventCode=4624" endswith="EventCode=4634" maxspan=-1 You may also be interested using LepideAuditor suite that helps to get historical logon/logoff reports into real time and filter the reports as per needs. Step 2: Track Active Directory User Login history using Event logs, How to Use Lepide Active Directory Auditor to check User Logon History, How to identify the source of Account Lockouts in Active Directory, How to Audit Successful Logon/Logoff and Failed Logons in Active Directory, How to enable the Security Auditing of Active Directory, Logon (Whenever an account is successfully logged on), Logoff (When an account is successfully logged off), How to Track User Logon History in Active Directory. You can also search for these event IDs. At the Run prompt or in Command Prompt, run the following command to update the group policies. Added new command-line options: /Source , /Server , /ExternalFolder. https://answers.splunk.com/answers/127012/how-can-i-use-windows-events-to-monitor-logon-sessions.htm https://answers.splunk.com/answers/101366/collecting-logon-logoff-logs-from-active-directory-and-put BSides Splunk 2022 Call for Papers is Open Until August 12. I'll report back on what I find. Repeat the steps for Audit Logoff and Audit Other Logon/Logoff policies. When connecting a remote computer and the 'Use New Event Log API' option is turned on, the loading process is now much faster than the previous versions. | eval Logofftime=_time+duration with a big THANK YOU. If you don't specify this option, the list is sorted according to the last sort that you made from the user interface. This topic has been locked by an administrator and is no longer open for commenting. {Source Computer, Terminated Time, Message, Workstation Name, Logon Type, Logon Duration, Remarks, Client Host Name, Client IP Address, Radius Client IP Address, Radius Client Host Name, Event Type, Logoff Time, Logon Time, When, User Name, CALLER PROCESS NAME, Domain}, Privileges required for event log collection, Privileges required for automatic auditing configuration, Privileges required for file server auditing, Configuring Audit Policies for Active Directory Auditing, Configuring SACLs for Active Directory Auditing, Configuring Audit Policies for File Server Auditing, Configuring Audit Policies for Member Server Auditing, Configuring Audit Policies for Workstation Auditing, Configuring Audit Policies for NetApp Filer Auditing, Configuring SACLs for NetApp Filers Auditing, Configuring Audit Policies for NetApp Cluster Auditing, Migrating data between different versions of MS SQL, Moving ADAudit Plus from one server/drive to another, Migrating ADAudit Plus from 32-bit to 64-bit architecture. Find articles, code and a community of database experts. Just yesterday I had a user request logon/logoff data on of his subordinates. Please be sure to post back what you find I don't have to reinvent this wheel. I'm notkeen on paying for a solution either, since it's unlikely I'll get this request again soon. Tweakedwentholdresponse to include more EventCodes. Note: We recommend that you create a new GPO, link it to the domain and edit it.
Real user, and synthetic monitoring of web applications from outside the firewall. WinLogOnView is also available in other languages. Go to Start All Programs Administrative Tools. You can put multiple /sort in the command-line if you want to sort by multiple columns. Integrates with Dameware Remote Everywhere and the Orion Platform. Splunk, Splunk>, Turn Data Into Doing, Data-to-Everything, and D2E are trademarks or Understanding what your users are doing in your critical systems is a crucial part to identify potential security breaches/suspicious behavior. It may be positively correlated with a logon event using the Logon ID value. You can use it to gather those logs and run a Logon Sessions Report which should show you what you're looking for, provided the events are still in the Event Log. Modernize your service desk with cloud-based platform intelligent ticketing, service management, configuration management, asset management, knowledge base and portal, as well secure remote support. Also depending on the environment EventCode 4800|4801|4802 which is screen lock may be the closest thing to getting a log off time. Click on the Reports tab and select the Local Logon-Logoff tab on the left, to view the reports listing. Click here for instructions on how to enable JavaScript in your browser. Enable Auditing on the domain level by using Group Policy: Computer Configuration/Windows Settings/Security Settings/Local Policies/Audit Policy. This article was written by Yuval Sinay, Microsoft MVP. If your server doesnt have Active Directory deployed, these policies can also be configured at the local machine. AppOptics: Next-gen SaaS-based application performance & infrastructure monitoring. Filter Attributes in the Local Logon-Logoff Reports Category.
Audit "logon events" records logons on the PC(s) targeted by the policy and the results appear in the Security Log on that PC(s). So you would need to gather the workstation Security Event Logs. The Logon/Logoff reports generated by Lepide Active Directory Auditor mean that tracking user logon session time for single or multiple users is essentially an automated process.